[HV22.08] Santa’s Virus
A user by the name of HACKventSanta may be spreading viruses. But Santa would never do that! The elves want you to find more information about this filthy impersonator.

Solution
This challenge gave us a name and an image. Since it’s open source intelligence from classification, I analyzed the image and looked for the usual things like strings, binwalk, exiftool and stegsolve, but it revealed nothing.
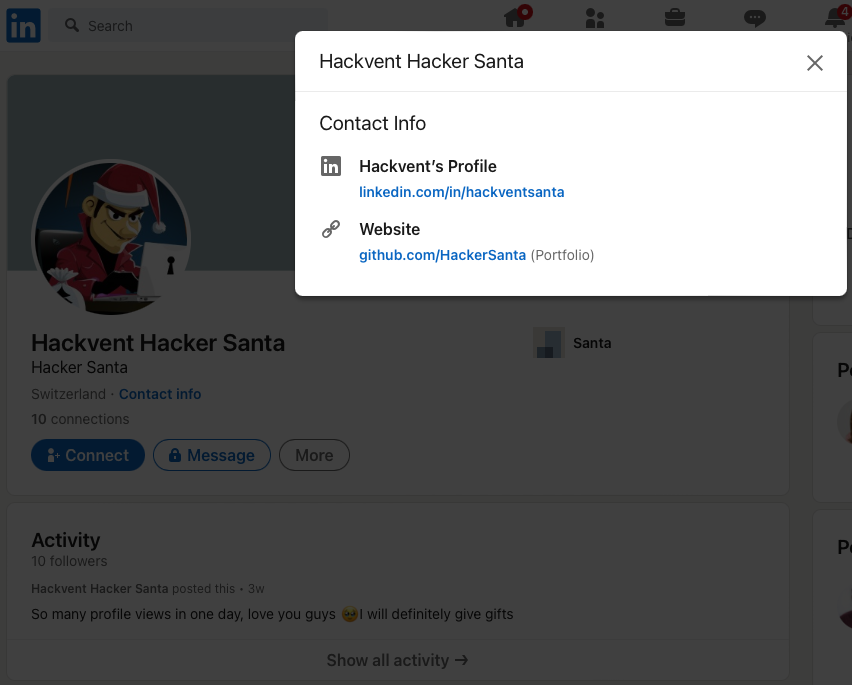
Next up was simply using a search engine for the name. Fotunately, in my case, DuckDuckGo immediately found an LinkedIn account. Now it only finds an Instagram account, but both lead to the same github.com user. Other users used tools like Sherlock to find the accounts.
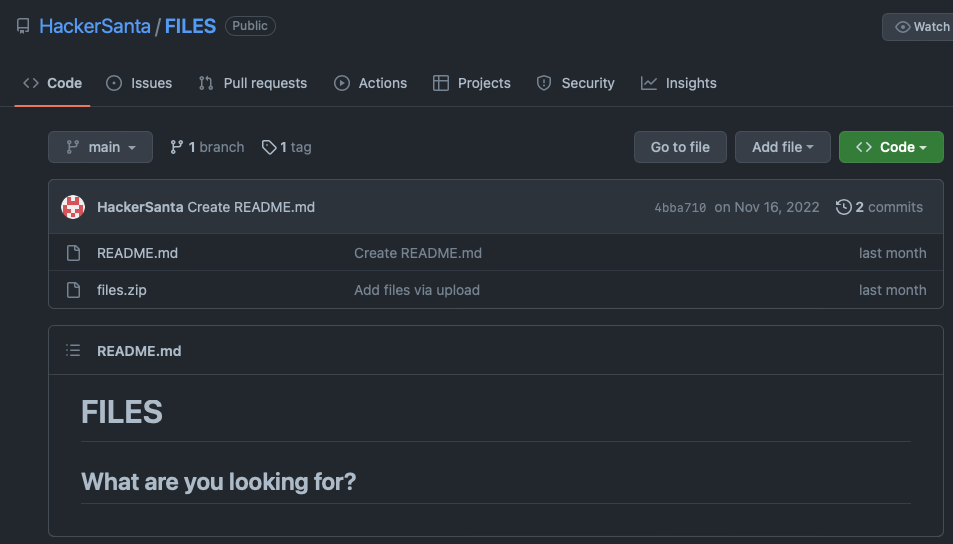
The only public repository (called FILES) has a rather empty README.md and a files.zip to offer, so I downloaded the files.zip and inspected it. It was rather boring (nothing hidden in it), just a simple index.html with a message No viruses alive here 🤔 cant say anything about tags.
Back to the repository, I noticed that there is 1 tag, and given the obvious hint, I looked into that.
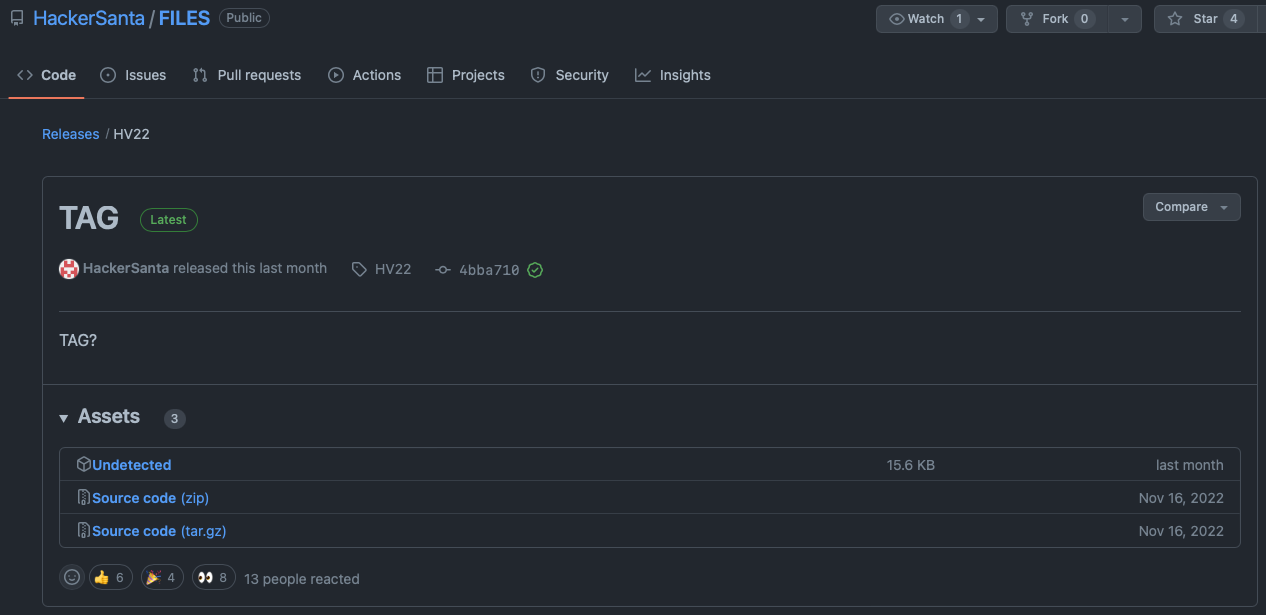
The tag TAG shows an additional asset called Undetected, which seems suspicious. I downloaded it and inspected it.
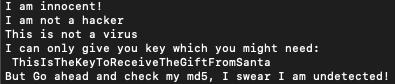
The file is an ELF 64-bit executable and reveals some interesting strings without letting it run.
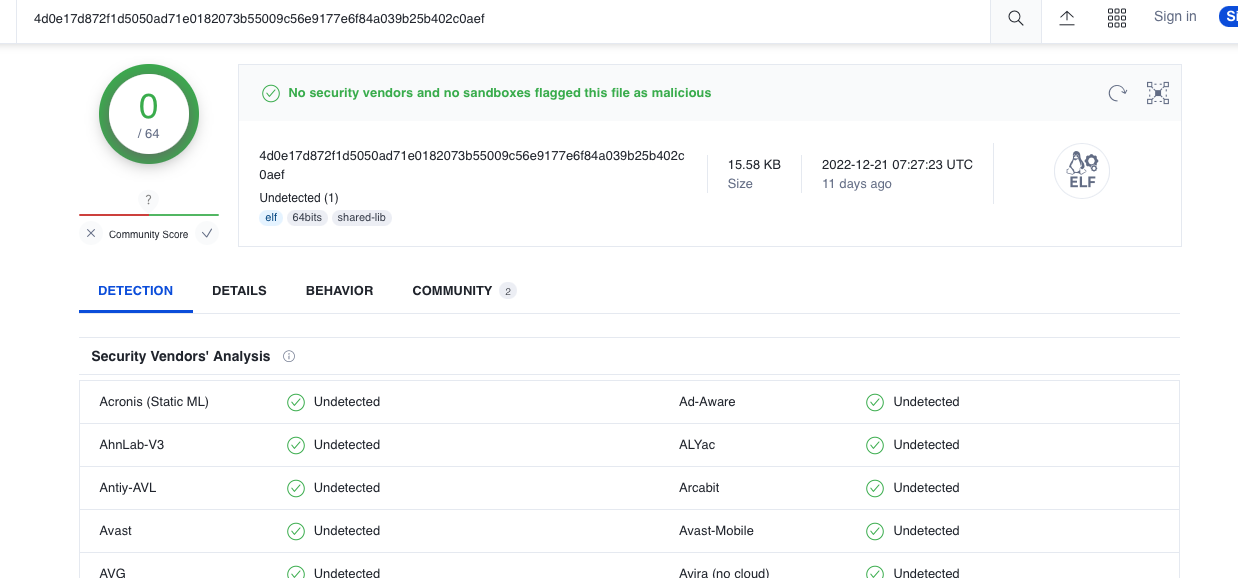
This hints to checking known virus databases for the file. And bingo, virustotal of course knows the file:
Scanning through the different sections of virustotal, I noticed that it had been uploaded with a few different names before:
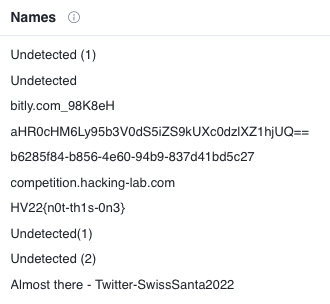
The fake flag wasn’t there when I originally solved the challenge, so I first went with the hint towards the twitter account @SwissSanta2022. It posted 3 QR codes. First one was (had to be) a rick roll. Second was a valid christimas song, third one finally was a link to a google drive which asks for a password.

There was another interesting thing inside the strings we found in the file, so I tried using ThisIsTheKeyToReceiveTheGiftFromSanta as the key, which opened a file called SANTAAAAAAAA.pdf.

The string SFYyMntIT0hPK1NBTlRBK0dJVkVTK0ZMQUdTK05PVCtWSVJVU30= in the top looks like base64 (due to the padding with =), so I fired up cyberchef to test that theory, which got rewarded with the flag HV22{HOHO+SANTA+GIVES+FLAGS+NOT+VIRUS}
